[CVSS 5.3 Medium](https://www.first.org/cvss/calculator/4-0#CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:L/VI:N/VA:N/SC:N/SI:N/SA:N) -- The `/repos/{owner}/{repo}/issues/{index}/dependencies` APIs allow a user to link an issue in one repository as "depending upon" an issue in another repository. Forgejo's implementation had an incorrect permission check which would verify only that the user had write permissions on the issue being modified, and not on the issue it was linking to. Due to the incorrect permission check, it was possible to view limited information (the existence of, and title of) an issue in a private repository that the user does not have access to view. The permission check has been corrected to take into account visibility of the remote repository.
[CVSS 5.3 Medium](https://www.first.org/cvss/calculator/4-0#CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:L/VI:N/VA:N/SC:N/SI:N/SA:N) -- Fetching information about a release via the `/repos/{owner}/{repo}/releases/tag/{tag}` API endpoint did not check whether the release was a draft, allowing accessing to information about a draft release to users who could predict an upcoming release tag but didn't have access to view it. The missing check has been added, returning a 404 response when the release is not published.
[CVSS 6.3 Medium](https://www.first.org/cvss/calculator/4-0#CVSS:4.0/AV:N/AC:L/AT:P/PR:N/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N) -- Forgejo's web interface allows deleting tags on a git repository through a form post. The endpoint for this form post had misconfigured middleware handlers which enforce security rights, allowing an anonymous user, or a logged-in user without the correct permissions, to delete tags on repositories that they did not own by injecting arbitrary internal tag identifiers into the form. The middleware handler configuration has been corrected.
[CVSS 2.1 Low](https://www.first.org/cvss/calculator/4-0#CVSS:4.0/AV:N/AC:L/AT:P/PR:H/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N) -- When the head branch of a pull request matches a branch protection rule, the head branch should be able to be merged or rebased only according to the "Push" rules defined in the protection rule. An implementation error checked those branch protection rules in the context of the base repository rather than the head repository, allowing users with write access to the base repository to be considered able to push to the branch, bypassing the "Enable push" option's expected security control.
[CVSS 2.1 Low](https://www.first.org/cvss/calculator/4-0#CVSS:4.0/AV:N/AC:L/AT:P/PR:H/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N) -- An issue owner can manipulate form inputs to delete the content history of comments they did not create, as long as those comments are on issues that they own. Although comment content is not affected, the history of edits on the comment can be trimmed. The validation in the form handler was corrected.
[CVSS 5.1 Medium](https://www.first.org/cvss/calculator/4-0#CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N) -- When a repository is configured with tag protection rules, it should not be possible for a user that is outside the whitelisted users or teams from modifying the protected tags. An incorrect parameter being passed to a security verification method allowed a user with write access to the repo to delete tags even if they were protected, as long as the tag was originally created by a user who is still authorized by the protection rules.
<!--start release-notes-assistant-->
## Release notes
<!--URL:https://codeberg.org/forgejo/forgejo-->
- Security bug fixes
- [PR](https://codeberg.org/forgejo/forgejo/pulls/10037): <!--number 10037 --><!--line 0 --><!--description Zml4KGFwaSk6IGZpeCBkZXBlbmRlbmN5IHJlcG8gcGVybXMgaW4gQ3JlYXRlL1JlbW92ZUlzc3VlRGVwZW5kZW5jeQ==-->fix(api): fix dependency repo perms in Create/RemoveIssueDependency<!--description-->
- [PR](https://codeberg.org/forgejo/forgejo/pulls/10037): <!--number 10037 --><!--line 1 --><!--description Zml4KGFwaSk6IGRyYWZ0IHJlbGVhc2VzIGNvdWxkIGJlIHJlYWQgYmVmb3JlIGJlaW5nIHB1Ymxpc2hlZA==-->fix(api): draft releases could be read before being published<!--description-->
- [PR](https://codeberg.org/forgejo/forgejo/pulls/10037): <!--number 10037 --><!--line 2 --><!--description bWlzY29uZmlndXJlZCBzZWN1cml0eSBjaGVja3Mgb24gdGFnIGRlbGV0ZSB3ZWIgZm9ybQ==-->misconfigured security checks on tag delete web form<!--description-->
- [PR](https://codeberg.org/forgejo/forgejo/pulls/10037): <!--number 10037 --><!--line 3 --><!--description aW5jb3JyZWN0IGxvZ2ljIGluICJVcGRhdGUgUFIiIGRpZCBub3QgZW5mb3JjZSBoZWFkIGJyYW5jaCBwcm90ZWN0aW9uIHJ1bGVzIGNvcnJlY3RseQ==-->incorrect logic in "Update PR" did not enforce head branch protection rules correctly<!--description-->
- [PR](https://codeberg.org/forgejo/forgejo/pulls/10037): <!--number 10037 --><!--line 4 --><!--description aXNzdWUgb3duZXIgY2FuIGRlbGV0ZSBhbm90aGVyIHVzZXIncyBjb21tZW50J3MgZWRpdCBoaXN0b3J5IG9uIHNhbWUgaXNzdWU=-->issue owner can delete another user's comment's edit history on same issue<!--description-->
- [PR](https://codeberg.org/forgejo/forgejo/pulls/10037): <!--number 10037 --><!--line 5 --><!--description dGFnIHByb3RlY3Rpb24gcnVsZXMgY2FuIGJlIGJ5cGFzc2VkIGR1cmluZyB0YWcgZGVsZXRlIG9wZXJhdGlvbg==-->tag protection rules can be bypassed during tag delete operation<!--description-->
<!--end release-notes-assistant-->
Co-authored-by: Joshua Rogers <MegaManSec@users.noreply.github.com>
Reviewed-on: https://codeberg.org/forgejo/forgejo/pulls/10037
Reviewed-by: 0ko <0ko@noreply.codeberg.org>
Co-authored-by: Mathieu Fenniak <mathieu@fenniak.net>
Co-committed-by: Mathieu Fenniak <mathieu@fenniak.net>
- Use the forked [binding](https://code.forgejo.org/go-chi/binding)
library. This library has two benefits, it removes the usage of
`github.com/goccy/go-json` (has no benefit as the minimo library is also
using it). It adds the `TrimSpace` feature, which will during the
binding part trim the spaces around the value it got from the form, this
is done before validation.
The CORS code has been unmaintained for long time, and the behavior is
not correct.
This PR tries to improve it. The key point is written as comment in
code. And add more tests.
Fix#28515Fix#27642Fix#17098
Fix#25473
Although there was `m.Post("/login/oauth/access_token", CorsHandler()...`,
it never really worked, because it still lacks the "OPTIONS" handler.
To mock a handler:
```go
web.RouteMock(web.MockAfterMiddlewares, func(ctx *context.Context) {
// ...
})
defer web.RouteMockReset()
```
It helps:
* Test the middleware's behavior (assert the ctx.Data, etc)
* Mock the middleware's behavior (prepare some context data for handler)
* Mock the handler's response for some test cases, especially for some
integration tests and e2e tests.
1. The "web" package shouldn't depends on "modules/context" package,
instead, let each "web context" register themselves to the "web"
package.
2. The old Init/Free doesn't make sense, so simplify it
* The ctx in "Init(ctx)" is never used, and shouldn't be used that way
* The "Free" is never called and shouldn't be called because the SSPI
instance is shared
---------
Co-authored-by: Giteabot <teabot@gitea.io>
Partially for #24457
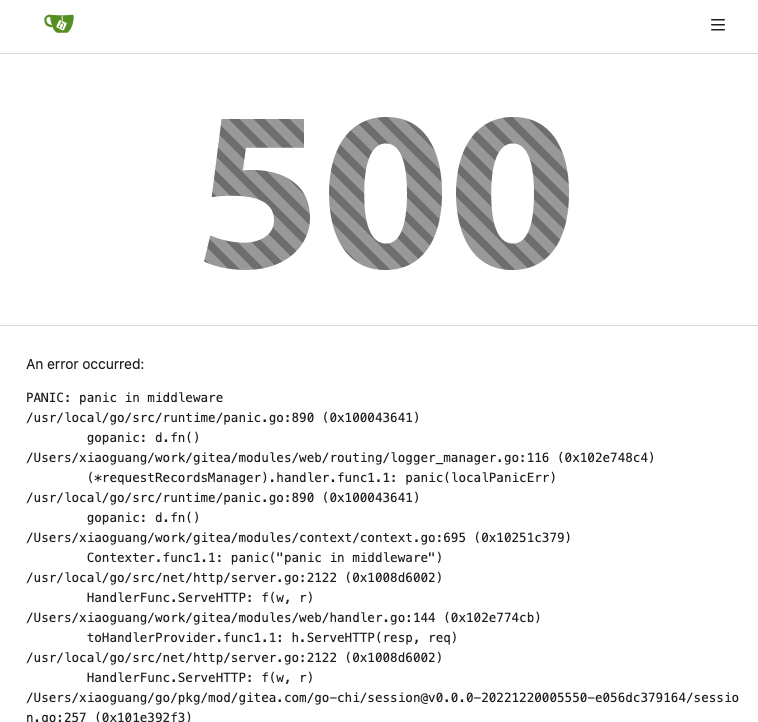
Major changes:
1. The old `signedUserNameStringPointerKey` is quite hacky, use
`ctx.Data[SignedUser]` instead
2. Move duplicate code from `Contexter` to `CommonTemplateContextData`
3. Remove incorrect copying&pasting code `ctx.Data["Err_Password"] =
true` in API handlers
4. Use one unique `RenderPanicErrorPage` for panic error page rendering
5. Move `stripSlashesMiddleware` to be the first middleware
6. Install global panic recovery handler, it works for both `install`
and `web`
7. Make `500.tmpl` only depend minimal template functions/variables,
avoid triggering new panics
Screenshot:
<details>
</details>
The old code is unnecessarily complex, and has many misuses.
Old code "wraps" a lot, wrap wrap wrap, it's difficult to understand
which kind of handler is used.
The new code uses a general approach, we do not need to write all kinds
of handlers into the "wrapper", do not need to wrap them again and
again.
New code, there are only 2 concepts:
1. HandlerProvider: `func (h any) (handlerProvider func (next)
http.Handler)`, it can be used as middleware
2. Use HandlerProvider to get the final HandlerFunc, and use it for
`r.Get()`
And we can decouple the route package from context package (see the
TODO).
# FAQ
## Is `reflect` safe?
Yes, all handlers are checked during startup, see the `preCheckHandler`
comment. If any handler is wrong, developers could know it in the first
time.
## Does `reflect` affect performance?
No. https://github.com/go-gitea/gitea/pull/24080#discussion_r1164825901
1. This reflect code only runs for each web handler call, handler is far
more slower: 10ms-50ms
2. The reflect is pretty fast (comparing to other code): 0.000265ms
3. XORM has more reflect operations already
Change all license headers to comply with REUSE specification.
Fix#16132
Co-authored-by: flynnnnnnnnnn <flynnnnnnnnnn@github>
Co-authored-by: John Olheiser <john.olheiser@gmail.com>
Make router logger more friendly, show the related function name/file/line.
[BREAKING]
This PR substantially changes the logging format of the router logger. If you use this logging for monitoring e.g. fail2ban you will need to update this to match the new format.
This PR continues the work in #17125 by progressively ensuring that git
commands run within the request context.
This now means that the if there is a git repo already open in the context it will be used instead of reopening it.
Signed-off-by: Andrew Thornton <art27@cantab.net>
* Clean-up HookPreReceive and restore functionality for pushing non-standard refs
There was an inadvertent breaking change in #15629 meaning that notes refs and other
git extension refs will be automatically rejected.
Further following #14295 and #15629 the pre-recieve hook code is untenably long and
too complex.
This PR refactors the hook code and removes the incorrect forced rejection of
non-standard refs.
Fix#16688
Signed-off-by: Andrew Thornton <art27@cantab.net>
Unfortunately the chi changes have resulted in the CORS headers for the
git smart http protocol going missing.
This is mostly because the OPTIONS method is not being handled by
httpBase anymore.
This PR adds a GetOptions, PostOptions and Options methods to web
handler to allow OPTIONS method requests to still reach the httpBase
function.
Fix#16350Close#16491
Signed-off-by: Andrew Thornton <art27@cantab.net>
Co-authored-by: Lunny Xiao <xiaolunwen@gmail.com>
There was a mistake in #15372 where deferral of gitrepo close occurs before it should.
This PR fixes this.
Signed-off-by: Andrew Thornton <art27@cantab.net>
Whilst doing other work I have noticed that there is an issue with Wrap when passing an
http.Handler - the next should be the next handler in line not empty.
Signed-off-by: Andrew Thornton <art27@cantab.net>
Use [chi](https://github.com/go-chi/chi) instead of the forked [macaron](https://gitea.com/macaron/macaron). Since macaron and chi have conflicts with session share, this big PR becomes a have-to thing. According my previous idea, we can replace macaron step by step but I'm wrong. :( Below is a list of big changes on this PR.
- [x] Define `context.ResponseWriter` interface with an implementation `context.Response`.
- [x] Use chi instead of macaron, and also a customize `Route` to wrap chi so that the router usage is similar as before.
- [x] Create different routers for `web`, `api`, `internal` and `install` so that the codes will be more clear and no magic .
- [x] Use https://github.com/unrolled/render instead of macaron's internal render
- [x] Use https://github.com/NYTimes/gziphandler instead of https://gitea.com/macaron/gzip
- [x] Use https://gitea.com/go-chi/session which is a modified version of https://gitea.com/macaron/session and removed `nodb` support since it will not be maintained. **BREAK**
- [x] Use https://gitea.com/go-chi/captcha which is a modified version of https://gitea.com/macaron/captcha
- [x] Use https://gitea.com/go-chi/cache which is a modified version of https://gitea.com/macaron/cache
- [x] Use https://gitea.com/go-chi/binding which is a modified version of https://gitea.com/macaron/binding
- [x] Use https://github.com/go-chi/cors instead of https://gitea.com/macaron/cors
- [x] Dropped https://gitea.com/macaron/i18n and make a new one in `code.gitea.io/gitea/modules/translation`
- [x] Move validation form structs from `code.gitea.io/gitea/modules/auth` to `code.gitea.io/gitea/modules/forms` to avoid dependency cycle.
- [x] Removed macaron log service because it's not need any more. **BREAK**
- [x] All form structs have to be get by `web.GetForm(ctx)` in the route function but not as a function parameter on routes definition.
- [x] Move Git HTTP protocol implementation to use routers directly.
- [x] Fix the problem that chi routes don't support trailing slash but macaron did.
- [x] `/api/v1/swagger` now will be redirect to `/api/swagger` but not render directly so that `APIContext` will not create a html render.
Notices:
- Chi router don't support request with trailing slash
- Integration test `TestUserHeatmap` maybe mysql version related. It's failed on my macOS(mysql 5.7.29 installed via brew) but succeed on CI.
Co-authored-by: 6543 <6543@obermui.de>